热门标签
热门文章
- 1CANoe用CAPL编程截取CAN Log_canoe的logging模块保存的日志类型
- 2机械狗还会给植物浇水?搭载OAK相机让机械狗拥有识别视觉的能力!_斯坦福大学机械狗
- 3“2020新冠肺炎记忆”登顶GitHub趋势榜!永不消逝的记忆却没有一行代码
- 4【QT教程】QT6界面美化进阶 QT界面美化
- 5AI顶流OpenAI又一重磅力作Sora,究竟是什么?一文弄懂Sora:简介|发展历程|主要功能|使用场景|替代软件|AI软件工具推荐!_aisora
- 6通过Java和Vue实现pdf的预览和下载_vuejava下载pdf
- 7重磅!多模态大模型最新综述!
- 8SpringCloud之RabbitMQ
- 9Yolov5由升级引起的报错:AttributeError: ‘Upsample‘ object has no attribute ‘recompute_scale_factor‘_("'{}' object has no attribute '{}'".format( attri
- 10Swagger笔记—Swagger3详细配置_swagger3配置
当前位置: article > 正文
It was possible to detect the usage of the deprecated TLSv1.0 and/or TLSv1.1 protocol on this system_tls version 1.1 protocol deprecated
作者:你好赵伟 | 2024-07-12 20:10:04
赞
踩
tls version 1.1 protocol deprecated
漏洞描述:
It was possible to detect the usage of the deprecated TLSv1.0 and/or TLSv1.1 protocol on this system.
Medium 9001/tcp
Medium (CVSS: 4.3)
NVT: SSL/TLS: Deprecated TLSv1.0 and TLSv1.1 Protocol Detection
Summary
It was possible to detect the usage of the deprecated TLSv1.0 and/or TLSv1.1 protocol on this system.
Vulnerability Detection Result
In addition to TLSv1.2+ the service is also providing the deprecated TLSv1.0 and
,→ TLSv1.1 protocols and supports one or more ciphers. Those supported ciphers c
,→an be found in the 'SSL/TLS: Report Supported Cipher Suites' (OID: 1.3.6.1.4.1
,→.25623.1.0.802067) VT.
Impact
An attacker might be able to use the known cryptographic aws to eavesdrop the connection
between clients and the service to get access to sensitive data transferred within the secured
connection.
Furthermore newly uncovered vulnerabilities in this protocols won't receive security updates
anymore.
Solution:
Solution type: Mitigation
It is recommended to disable the deprecated TLSv1.0 and/or TLSv1.1 protocols in favor of the
TLSv1.2+ protocols. Please see the references for more information.
Aected Software/OS
All services providing an encrypted communication using the TLSv1.0 and/or TLSv1.1 protocols.
Vulnerability Insight
The TLSv1.0 and TLSv1.1 protocols contain known cryptographic aws like:
. . . continues on next page . . .
2 RESULTS PER HOST 5
. . . continued from previous page . . .
- CVE-2011-3389: Browser Exploit Against SSL/TLS (BEAST)
- CVE-2015-0204: Factoring Attack on RSA-EXPORT Keys Padding Oracle On Downgraded
Legacy Encryption (FREAK)
Vulnerability Detection Method
Check the used TLS protocols of the services provided by this system.
Details: SSL/TLS: Deprecated TLSv1.0 and TLSv1.1 Protocol Detection
OID:1.3.6.1.4.1.25623.1.0.117274
Version used: 2021-07-19T08:11:48Z
References
cve: CVE-2011-3389
cve: CVE-2015-0204
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
解决办法:禁用已弃用的TLSv1.0和/或TLSv1.1协议,以支持TLSv1.2+协议。
TLS发展历史:
| 协议 | 发布时间 | 状态 |
|---|---|---|
| SSL 1.0 | 未公布 | 未公布 |
| SSL 2.0 | 1995年 | 已于2011年弃用 |
| SSL 3.0 | 1996年 | 已于2015年弃用 |
| TLS 1.0 | 1999年 | 于2021年弃用 |
| TLS 1.1 | 2006年 | 于2021年弃用 |
| TLS 1.2 | 2008年 | |
| TLS 1.3 | 2018年 |
1、Nginx配置
如果conf/nginx.conf配置了ssl证书,且default_server的server域里面版本如下
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
- 1
则删除TLS1.0 TLSv1.1、增加TLS1.3
ssl_protocols TLSv1.2 TLSv1.3;
- 1
修改完后,执行./sbin/nginx -s reload重载生效。
2、Apache配置
修改/usr/local/apache/conf/extra/httpd-ssl.conf文件
vi /usr/local/apache/conf/extra/httpd-ssl.conf
- 1
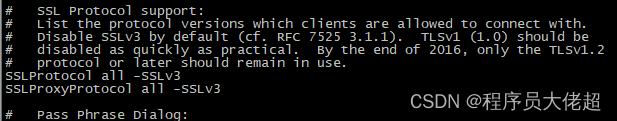
可以看到版本还是SSLv3,修改为如下
SSLProtocol -ALL +TLSv1.2 +TLSv1.3
SSLProxyProtocol -ALL +TLSv1.2 +TLSv1.3
- 1
- 2
重启Apache
/usr/local/apache/bin/apachectl restart
- 1
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/你好赵伟/article/detail/815796
推荐阅读
相关标签


