热门标签
热门文章
- 1基于ros-qt 开发ui界面完成标定工具包_标定界面ui
- 2RK3568技术笔记十五 固件烧写_rk3568固件解sr
- 3ES聚合查询详解(二):桶聚合_mindoccount
- 4自己电脑做服务器需要装什么系统,自己电脑做服务器需要什么配置
- 5在idea下terminal输入git的status命令后出现中文乱码\346\240\210/的解决办法_idea使用git status之后无法输入命令了
- 6【Yarn】系统架构&高可用_yarn采用的体系架构是主从结构,其中主节点是 ,从节点是 。
- 7大数据的5V特征分别是什么?_大数据5v特性
- 8各种对抗神经网络(GAN)大合集_gan non-overlapping
- 9git合并分支(一看就懂)_合并分支成功后显示啥页面
- 10程序猿214情人节专题----基于GitHub打造个人网站及Android的录制功能使用_android 录像github
当前位置: article > 正文
ctfer的web日常:给你shell (ctfshow)_easyshell ctf
作者:Li_阴宅 | 2024-07-10 20:52:45
赞
踩
easyshell ctf
目录
前期准备:
进入页面,发现没有什么信息:
查看源码,发现“/?view_source”路由:

访问此页面:
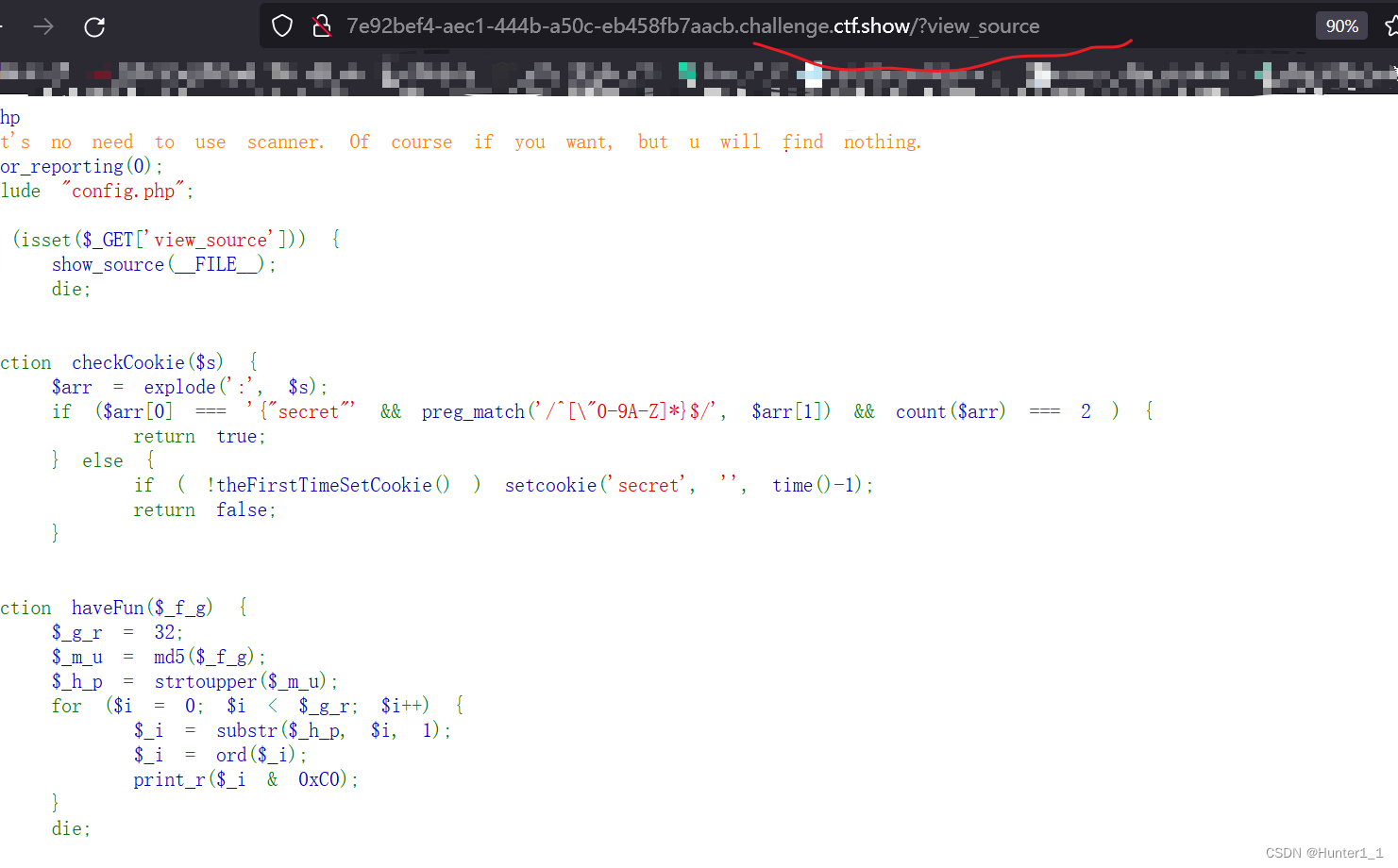
代码审计(1):
- <?php
- //It's no need to use scanner. Of course if you want, but u will find nothing.
- error_reporting(0);
- include "config.php";
-
- if (isset($_GET['view_source'])) {
- show_source(__FILE__); // 当参数为view_source即访问/?view_source时,展示__FILE__即我们看到的代码
- die;
- }
-
- function checkCookie($s) {
- $arr = explode(':', $s); // 以“:”进行分组,并将每一个部分存到数组arr
- if ($arr[0] === '{"secret"' && preg_match('/^[\"0-9A-Z]*}$/', $arr[1]) && count($arr) === 2 ) {
- return true; # arr[0] === {"secret" 且 $arr[1]必须包含数字字母至少一种
- } else {
- if ( !theFirstTimeSetCookie() ) setcookie('secret', '', time()-1);
- return false;
- }
- }
-
- function haveFun($_f_g) { // 对$_f_g进行MD5加密并转为大写字母,最后将每一位字符的ascii码值进行与运算
- $_g_r = 32;
- $_m_u = md5($_f_g);
- $_h_p = strtoupper($_m_u);
- for ($i = 0; $i < $_g_r; $i++) {
- $_i = substr($_h_p, $i, 1);
- $_i = ord($_i);
- print_r($_i & 0xC0);
- }
- die;
- }
-
- isset($_COOKIE['secret']) ? $json = $_COOKIE['secret'] : setcookie('secret', '{"secret":"' . strtoupper(md5('y1ng')) . '"}', time()+7200 );
- checkCookie($json) ? $obj = @json_decode($json, true) : die('no');
- // 判断有无secret
- // 通过secret赋值给$json,再通过$json建立$obj
- // json_decode() 将json格式的数据转换为对象,数组,转换为数组要加true
- // json的secret需要满足 checkCookie($s) 里面的条件
- if ($obj && isset($_GET['give_me_shell'])) {
- ($obj['secret'] != $flag_md5 ) ? haveFun($flag) : echo "here is your webshell: $shell_path";
- }
- /*要让传入的secret为 $flag_md5,这里就存在漏洞了,利用php的弱类型比较,但是这里又有个问题,在json_decode()返回""里面的内
- 容是字符串,就不能进行弱类型比较了,但是如果里面的内容,比如数字,没有被""括起来,返回的就是个int整数,所以注意把""删去,也
- 就是{"secret":123},这里开始没注意到还被坑了,一直没有爆破出来
- */
- die;

行动:
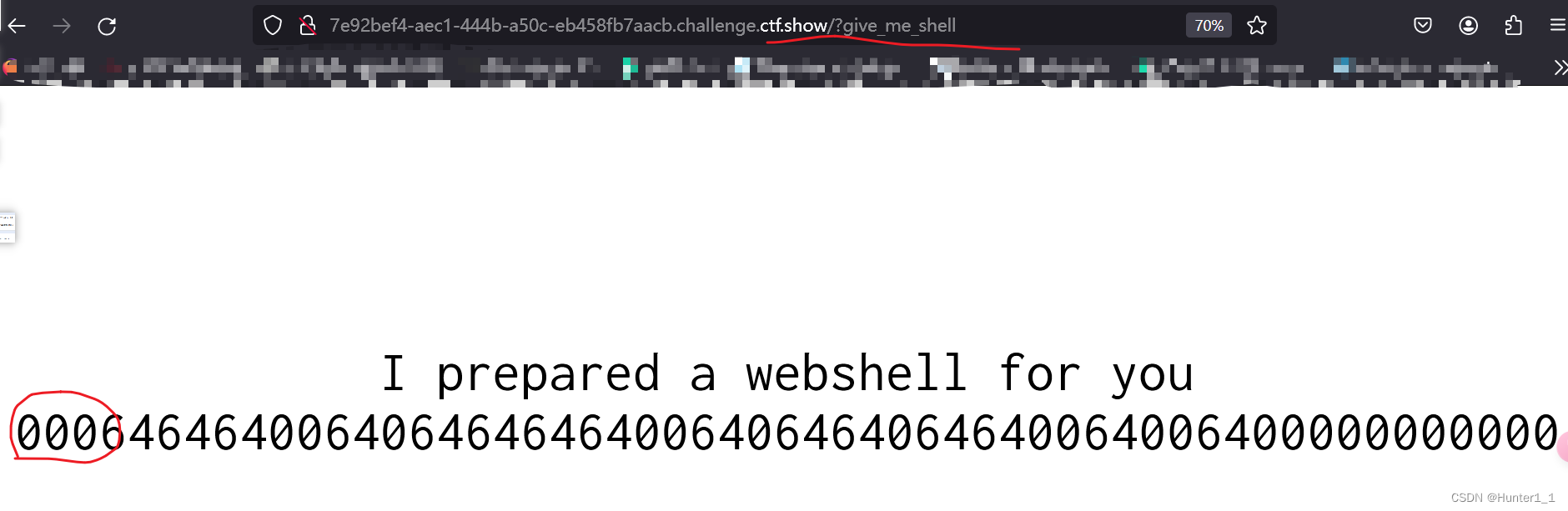
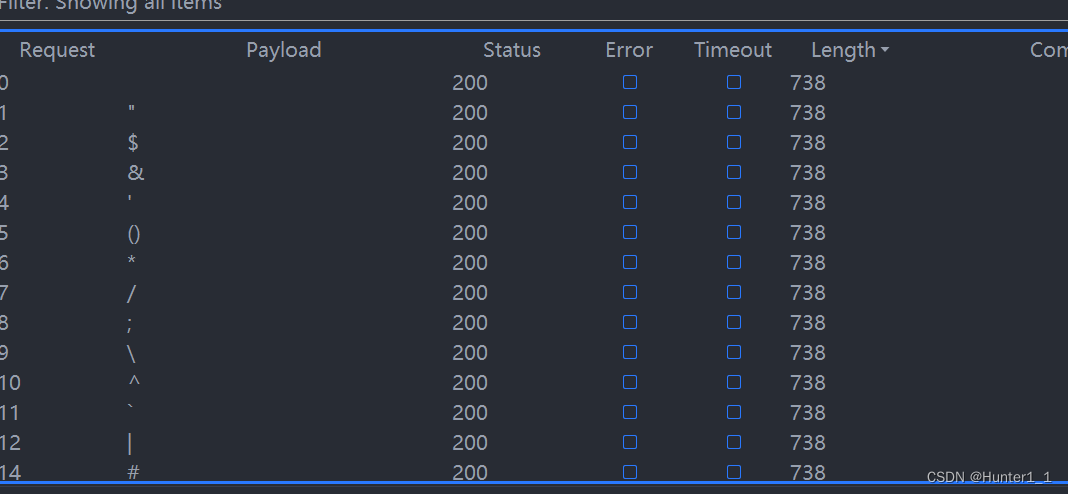
因为数字与0xC0为0;所有可以得知$flag_md5前3位为数字;再根据php弱类型比较的特性,如111 == ‘111adf’,用bp进行爆破:

故secret = 115满足$obj['secret'] != $flag_md5;
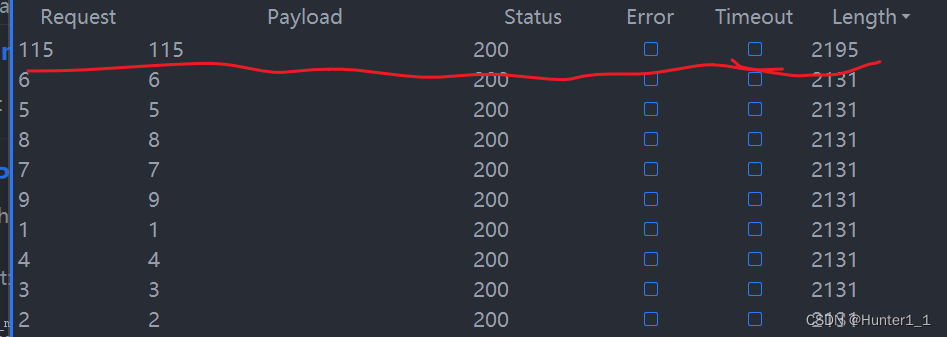
修改访问得:
访问w3b5HeLLlll123.php: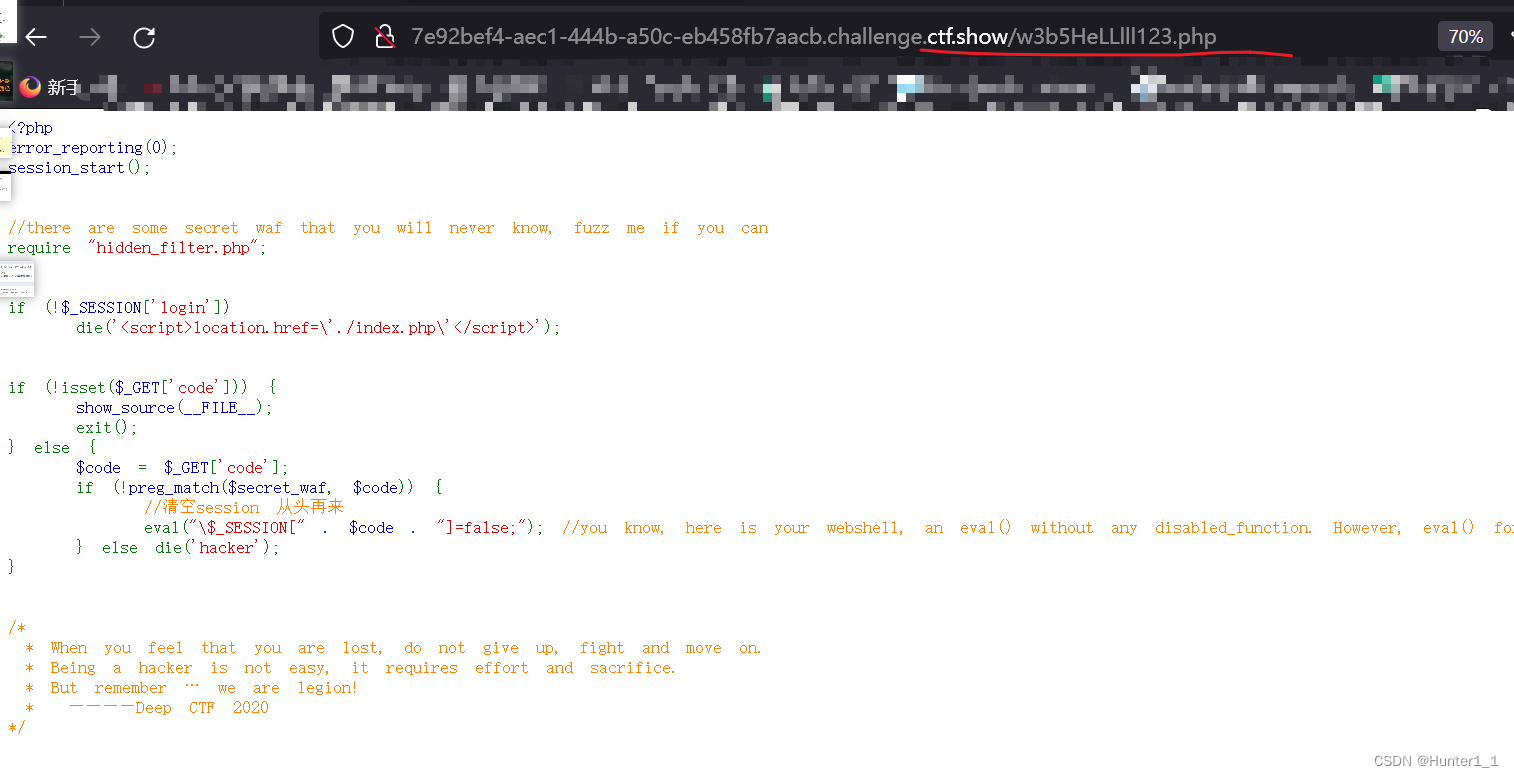
代码审计(2):
- <?php
- error_reporting(0);
- session_start();
-
-
- //there are some secret waf that you will never know, fuzz me if you can
- require "hidden_filter.php";
-
-
- if (!$_SESSION['login'])
- die('<script>location.href=\'./index.php\'</script>');
-
-
- if (!isset($_GET['code'])) {
- show_source(__FILE__);
- exit();
- } else {
- $code = $_GET['code'];
- if (!preg_match($secret_waf, $code)) {
- //清空session 从头再来
- eval("\$_SESSION[" . $code . "]=false;"); //you know, here is your webshell, an eval() without any disabled_function. However, eval() for $_SESSION only XDDD you noob hacker
- } else die('hacker');
- }
-
-
- /*
- * When you feel that you are lost, do not give up, fight and move on.
- * Being a hacker is not easy, it requires effort and sacrifice.
- * But remember … we are legion!
- * ————Deep CTF 2020
- */

发现好多东西都被禁了;
大佬:

声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/Li_阴宅/article/detail/807635
推荐阅读
- 0x01 WEB_你取吧题目源码[详细] -->
赞
踩
相关标签