热门标签
热门文章
- 1Flink开发-实现有状态的计算_flink有状态计算
- 2使用rkhunter Rootkit猎手检查Rootkit:全面指南_rootkit hunter
- 3根据《RabbitMQ实战--高效部署分布式消息队列》这本书来具体总结下_如何写一个高效的rabbitmq 队列
- 4决策树总结
- 5如何在面试中展现你对Python的coding能力?
- 6Arduino开发ESP32-CAM模块 & 使用Python-PyQt5编写图传.exe独立程序_auduino图传
- 7【C++综合项目】——基于Boost库的搜索引擎(手把手讲解,小白一看就会!!)_c++ boost
- 8小白学爬虫-进阶-PySpider操作指北
- 9PyQt 5主要类介绍_pyqt5 子类
- 10解决虚拟机下git出现Could not resolve proxy: https的错误_could not resolve proxy get 未知的错误
当前位置: article > 正文
RSA加密:Web前端登录账户密码加密传输_登录密码前端传输处理方法
作者:Guff_9hys | 2024-08-08 13:20:26
赞
踩
登录密码前端传输处理方法
一般在做系统时候对安全性要求比较高,现在通常选择https协议来进行数据传输。很多情况下一般的javaweb网站,如果安全要求不是很高的话,用https协议就可以了。在这种情况下,密码的明文传输显然是不合适的,因为请求如果在传输过程中被截了,就可以直接拿明文密码登录网站了。 为了传输数据的安全、今天就采用RSA加密方式来进行加密。
实现方式思路:
编写加解密公共方法类--公钥方法--前端在向后台发起登录请求之前,先请求后台获取公钥的方法,然后经过加密之后再发起登录请求--前端代码需引入jsencrypt.min.js文件--后端接收前端传输过来的密文进行解密--完成登录
完整代码实现:
后端首先引入加密jar包
- <!--需要导入的依赖jar-->
- <!-- https://mvnrepository.com/artifact/org.bouncycastle/bcprov-jdk16 -->
- <dependency>
- <groupId>org.bouncycastle</groupId>
- <artifactId>bcprov-jdk16</artifactId>
- <version>1.46</version>
- </dependency>
编写RSA加密工具类:
- package com.railway.common.utils;
- /**
- * Created by Administrator on 2022/2/8 0008.
- */
-
- import org.apache.commons.codec.binary.Base64;
- import org.bouncycastle.jce.provider.BouncyCastleProvider;
-
- import javax.crypto.Cipher;
- import java.security.*;
- import java.security.interfaces.RSAPublicKey;
-
- public class RSAUtil{
- private static final KeyPair keyPair = initKey();
- private static KeyPair initKey() {
- try {
- Provider provider =new BouncyCastleProvider();
- Security.addProvider(provider);
- SecureRandom random = new SecureRandom();
- KeyPairGenerator generator = KeyPairGenerator.getInstance("RSA", provider);
- generator.initialize(1024,random);
- return generator.generateKeyPair();
- } catch(Exception e) {
- throw new RuntimeException(e);
- }
- }
- private static byte[] decrypt(byte[] byteArray) {
- try {
- Provider provider = new org.bouncycastle.jce.provider.BouncyCastleProvider();
- Security.addProvider(provider);
- Cipher cipher = Cipher.getInstance("RSA/ECB/PKCS1Padding", provider);
- PrivateKey privateKey = keyPair.getPrivate();
- cipher.init(Cipher.DECRYPT_MODE, privateKey);
- byte[] plainText = cipher.doFinal(byteArray);
- return plainText;
- } catch(Exception e) {
- throw new RuntimeException(e);
- }
- }
- public static String decryptBase64(String string) {
- return new String(decrypt(Base64.decodeBase64(string.getBytes())));
- }
- public static String generateBase64PublicKey() {
- PublicKey publicKey = (RSAPublicKey)keyPair.getPublic();
- return new String(Base64.encodeBase64(publicKey.getEncoded()));
- }
-
- }
-
-
编写前端需要调用后端生成公钥方法接口:
- // 后端登录生成公钥方法
- @RequestMapping(value = "/getPublicKey", method = RequestMethod.GET)
- public R RSAKey(){
- String publicKey = RSAUtil.generateBase64PublicKey();
- return R.ok().put("publicKey",publicKey);
- }
前端向后台发送登录请求前,先向后台请求获取公钥,加密后再发起登录请求。
需要提前引入 jsencrypt.min.js文件或npm安装就行
- // 获取公钥
- export function encryption(username, password) {
- return new Promise((resolve, reject) => {
- PublicKey().then((res) => {
- console.log(res);
- let encrypt = new JSEncrypt(); //创建加密实例
- let PublicKey = res.publicKey;
- encrypt.setPublicKey(PublicKey);
- username = encrypt.encrypt(username);
- password = encrypt.encrypt(password);
- resolve({
- username: username,
- password: password
- })
- })
- })
- }
后端登录接收并解密:
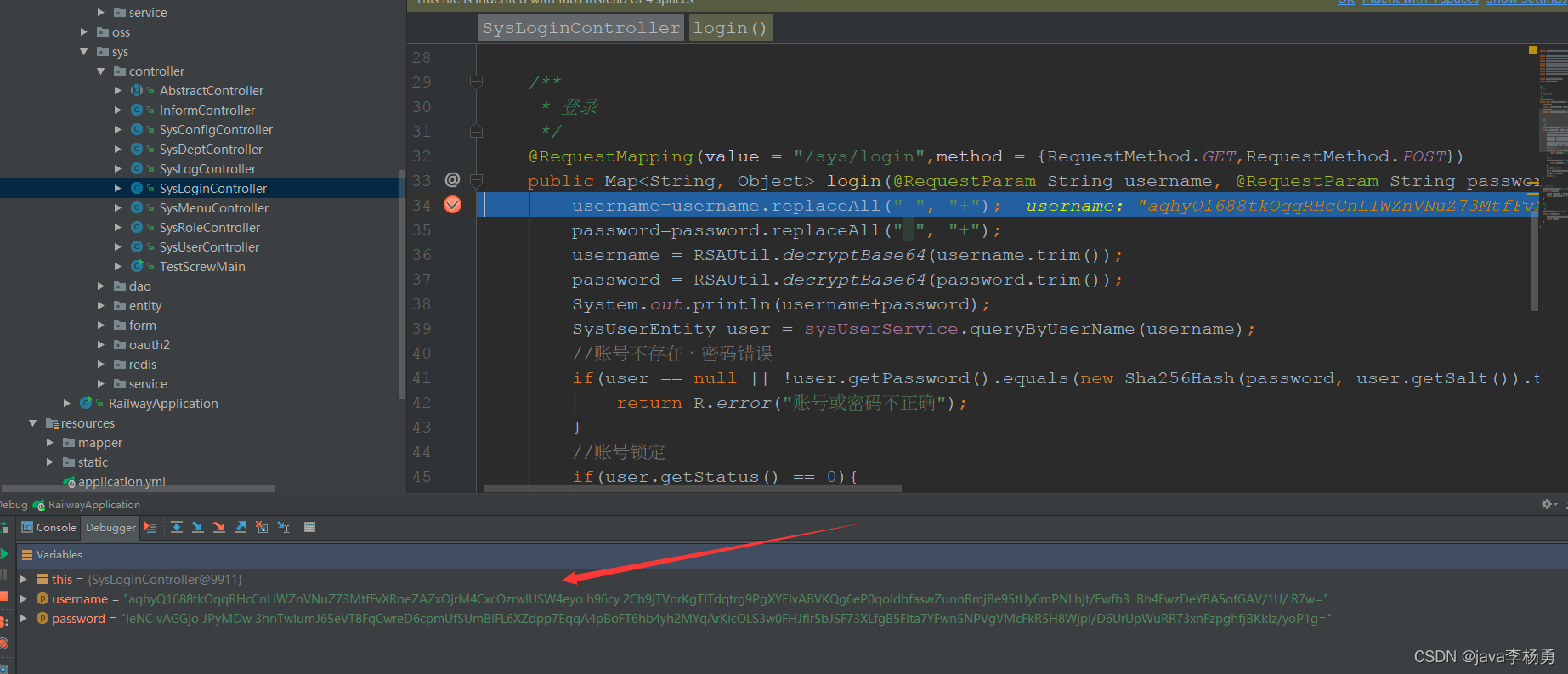
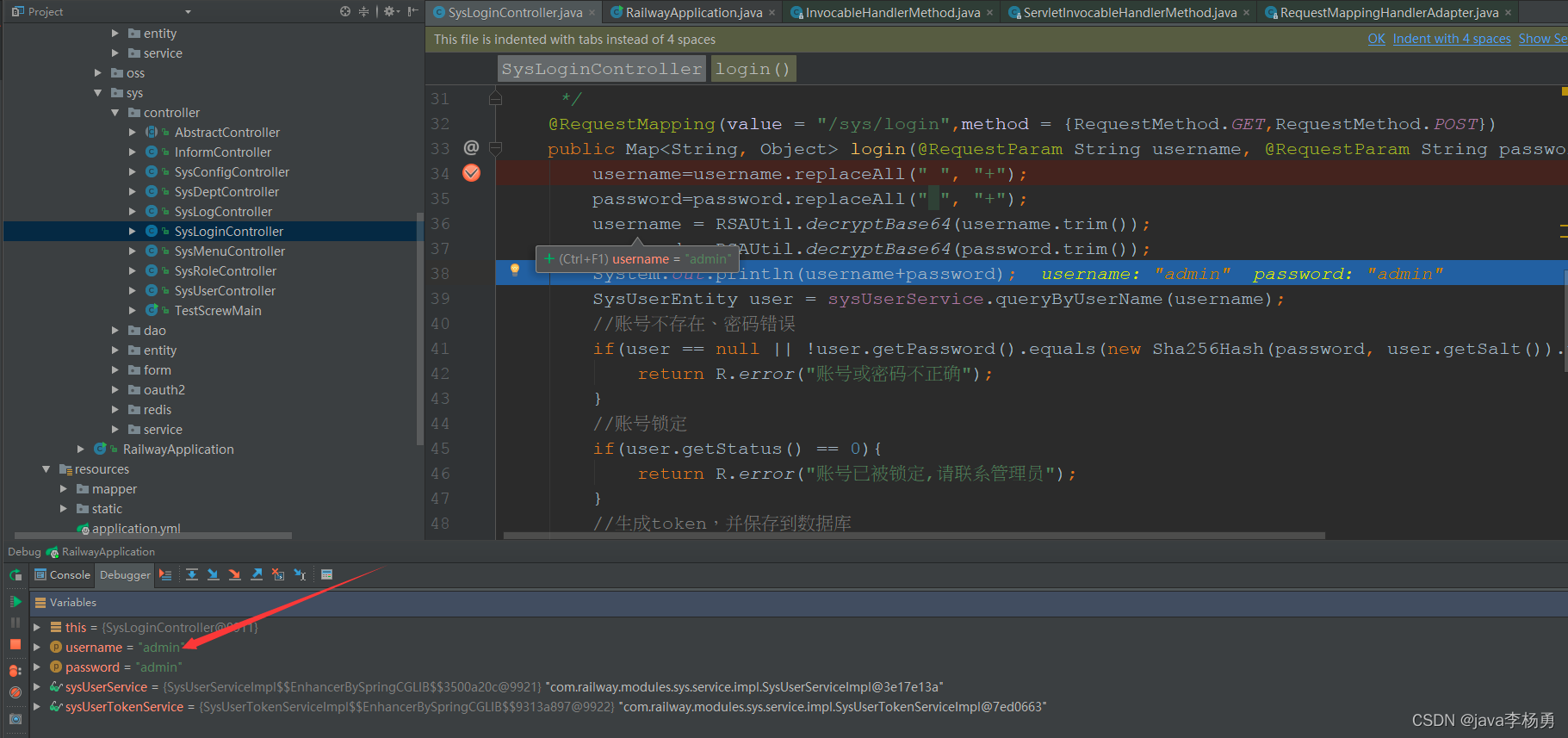
后端登录接口实现:
- /**
- * 登录
- */
- @RequestMapping(value = "/sys/login",method = {RequestMethod.GET,RequestMethod.POST})
- public Map<String, Object> login(@RequestParam String username, @RequestParam String password)throws IOException {username=username.replaceAll(" ", "+");
- password=password.replaceAll(" ", "+");
- username = RSAUtil.decryptBase64(username.trim());
- password = RSAUtil.decryptBase64(password.trim());
- System.out.println(username+password);
- SysUserEntity user = sysUserService.queryByUserName(username);
- //账号不存在、密码错误
- if(user == null || !user.getPassword().equals(new Sha256Hash(password, user.getSalt()).toHex())) {
- return R.error("账号或密码不正确");
- }
- //账号锁定
- if(user.getStatus() == 0){
- return R.error("账号已被锁定,请联系管理员");
- }
- //生成token,并保存到数据库
- R r = sysUserTokenService.createToken(user.getUserId());
- r.put("user",user);
- return r;
- }
源码获取:
大家点赞、收藏、关注、评论啦 、查看
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/Guff_9hys/article/detail/948433
推荐阅读
相关标签
Copyright © 2003-2013 www.wpsshop.cn 版权所有,并保留所有权利。


